Crypto Wallet Best Practices
Ready to manage your own keys? Here are the top crypto wallet best practices to help you out.
Managing your own keys requires work, caution, and discipline. And the dangers of slip-ups are all too real. Social media is littered with horror stories from people who have been scammed, hacked, and otherwise swindled out of their crypto.
This post should demystify the risks and clarify how you can secure your crypto effectively.
Not sure if managing your own keys is right for you? Check out our post Non-Custodial Wallet Pros and Cons.
Recovery phrase best practices
The recovery phrase for your wallet is the most critical item to safeguard with the best practices here.
Your recovery phrase (aka seed phrase) is the key to your crypto. More specifically, it is the master key for all of the crypto accounts and private keys on your wallet.
There are three reasons to use a recovery phrase:
- Recover from losing your hardware wallet.
- Clone your hardware wallet so you can have a secondary.
- Practice recovery.
Based on the first two, you can see why keeping the recovery key confidential is so critical.
What if someone else gets your recovery phrase?
Just like you, they can clone your wallet. This gives them full access to your crypto.
You will not be aware this has happened. This means if someone gets your recovery phrase today, they may take your crypto today. Or they may take it years from now.
Because of this, you need to protect your recovery phrase with the utmost responsibility.
It’s worth stating again:
- If you lose your hardware wallet, your computer, or your hard drive, your crypto is not lost. You can recover using your recovery phrase.
- On the flip side of that, if someone gets your recovery phrase, they’ll gain full access to your crypto, and most likely, you will lose all of it.
With that understanding, here are the best practices for your recovery phrase.
Phishing is constant are pervades many platforms. Your phrase is not needed to send or receive transactions.
Never give it out to a 3rd-party, such as an internet stranger, a technical support person, or otherwise. People from Trezor and Ledger will never ask you for your recovery phrase.
Likewise, it might be tempting to give a friend or relative your phrase as a backup. The problem is, they may, despite good intentions, not follow all of these best practices. The responsibility level is extremely high. It’s too much to place on other people.
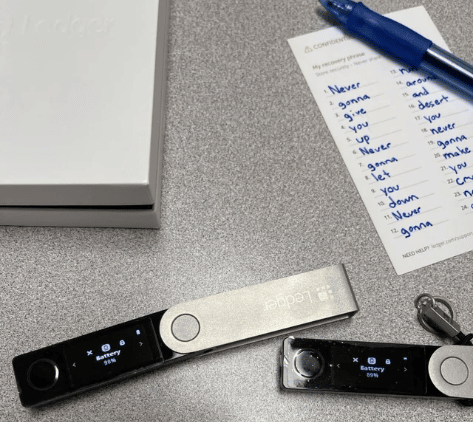
Never put your recovery phrase on a phone, computer, or online
Recovery phrases have a particular pattern. This means malicious programs can identify and capture them. It is even possible to extract them from pictures.
This is probably the most common form of crypto theft.
So:
- Don’t type your recovery phrase in Word, Google Docs, Notepad, etc…
- Don’t take a picture of your recovery phrase
- Don’t store your recovery phrase on a phone or computer
- Don’t type your recovery phrase
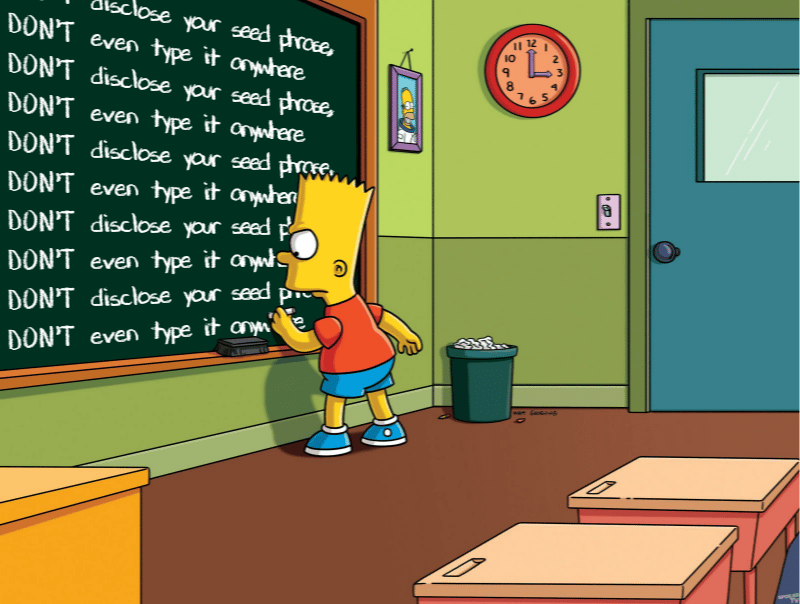
While this may seem extreme, keyloggers and similar malware are real. Even many trusted web applications have permission to read your typing. Data is shared. Employees go rogue. Mistakes are made. Your recovery phrase should not touch the digital world.
Based on this, using a hot wallet (internet-based wallet) immediately comes into question. They take different measures to improve security, but fundamentally, hot wallets cannot get around this best practice completely. See the hardware wallet section below.
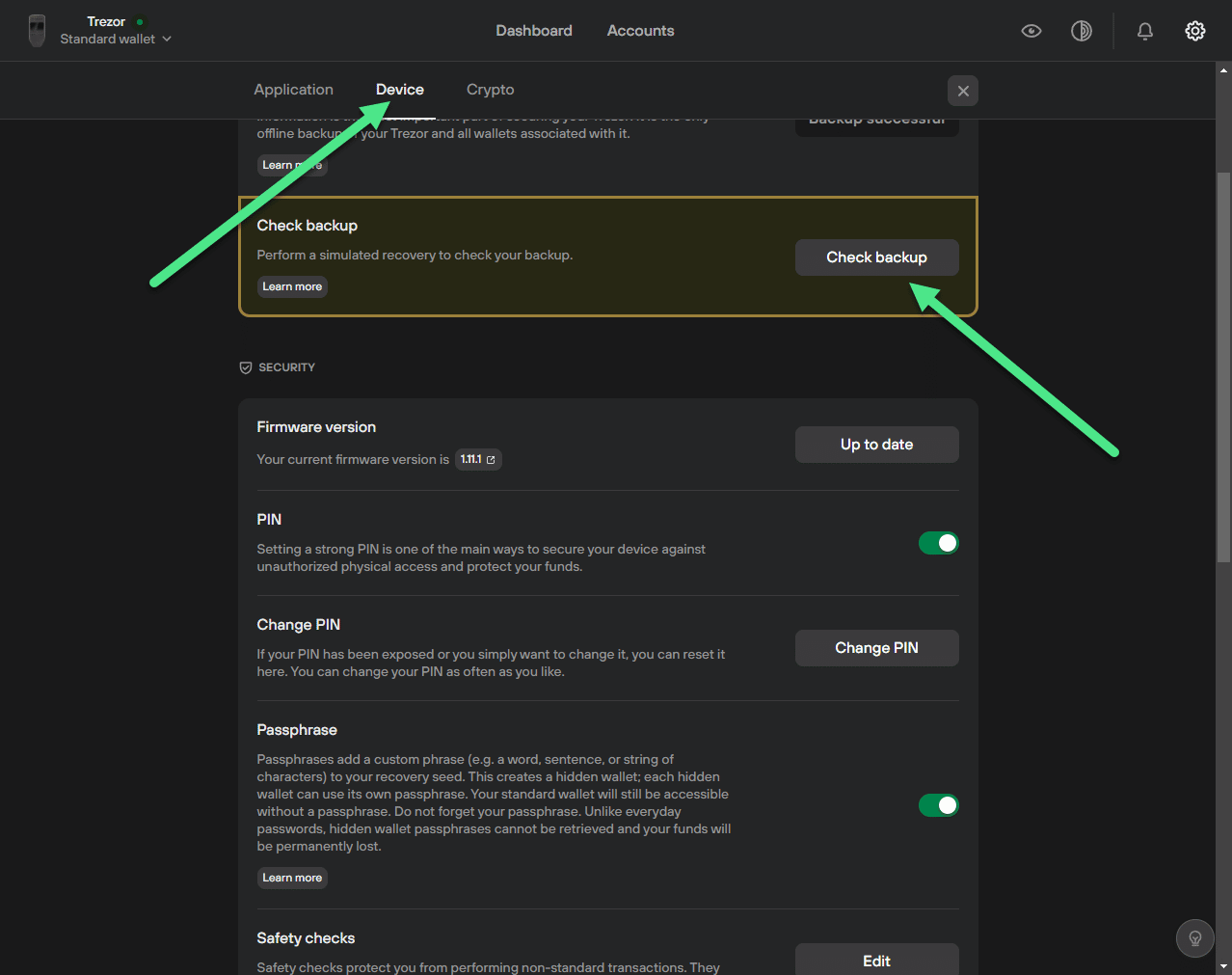
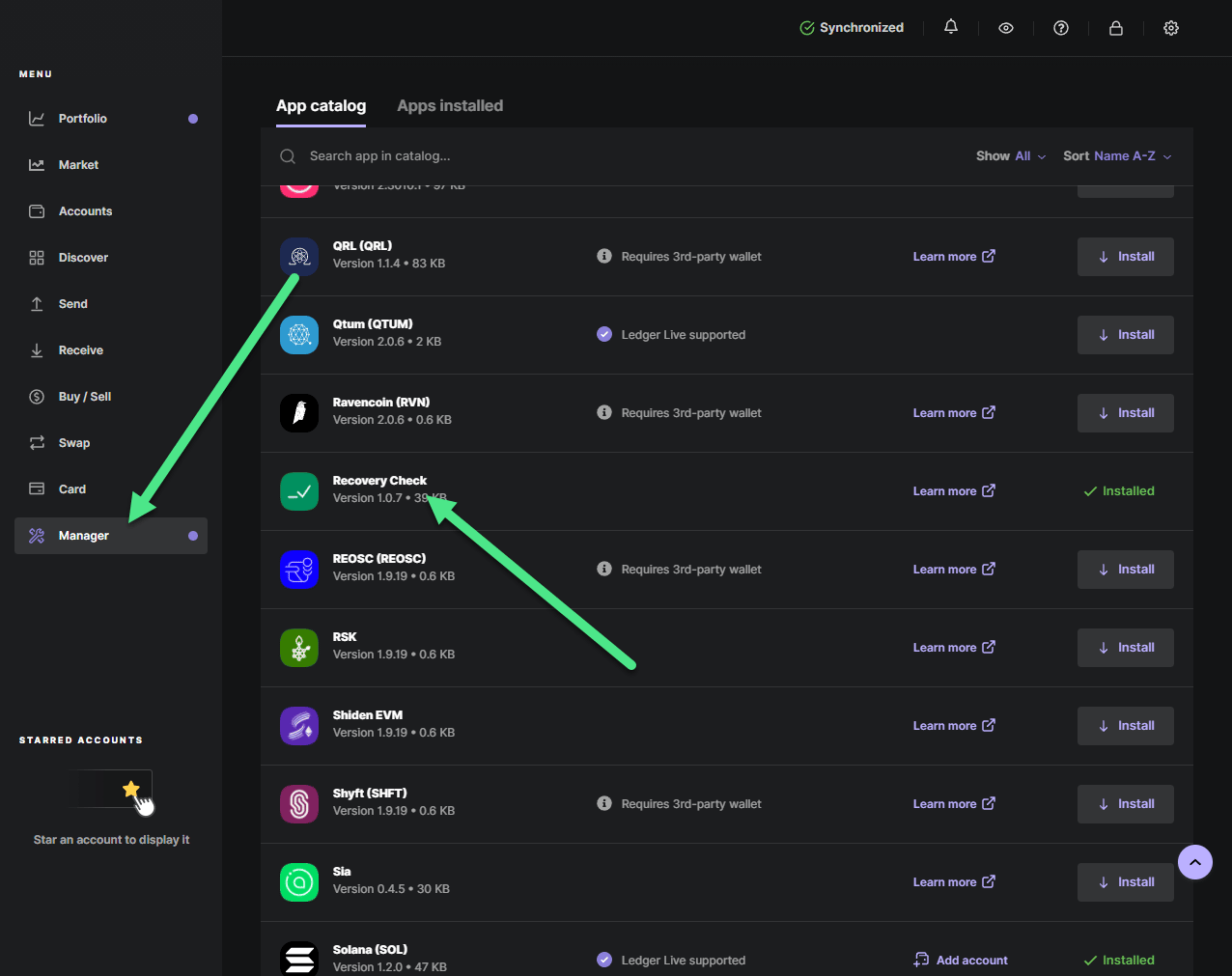
Practice recovery
Good wallets, including both Ledger and Trezor, give you the ability to practice recovery. This allows you to confirm your phrase and also walks you through the steps to build familiarity with the process.
A best practice is to perform practice recoveries once per month. If something fails, you need to move your crypto.
3-2-1 Backup
Your recovery phrase is your backup. Therefore, when handling it, you should follow standard 3-2-1 backup best practice.
- 3 copies of your data
- 2 on different media
- 1 offsite
Let’s unpack that a bit.
Having 3 copies of your recovery seed is straightforward.
Having 2 copies on different media means you may have (1) handwritten your seed on a piece of paper and (2) etched it into a seed card.
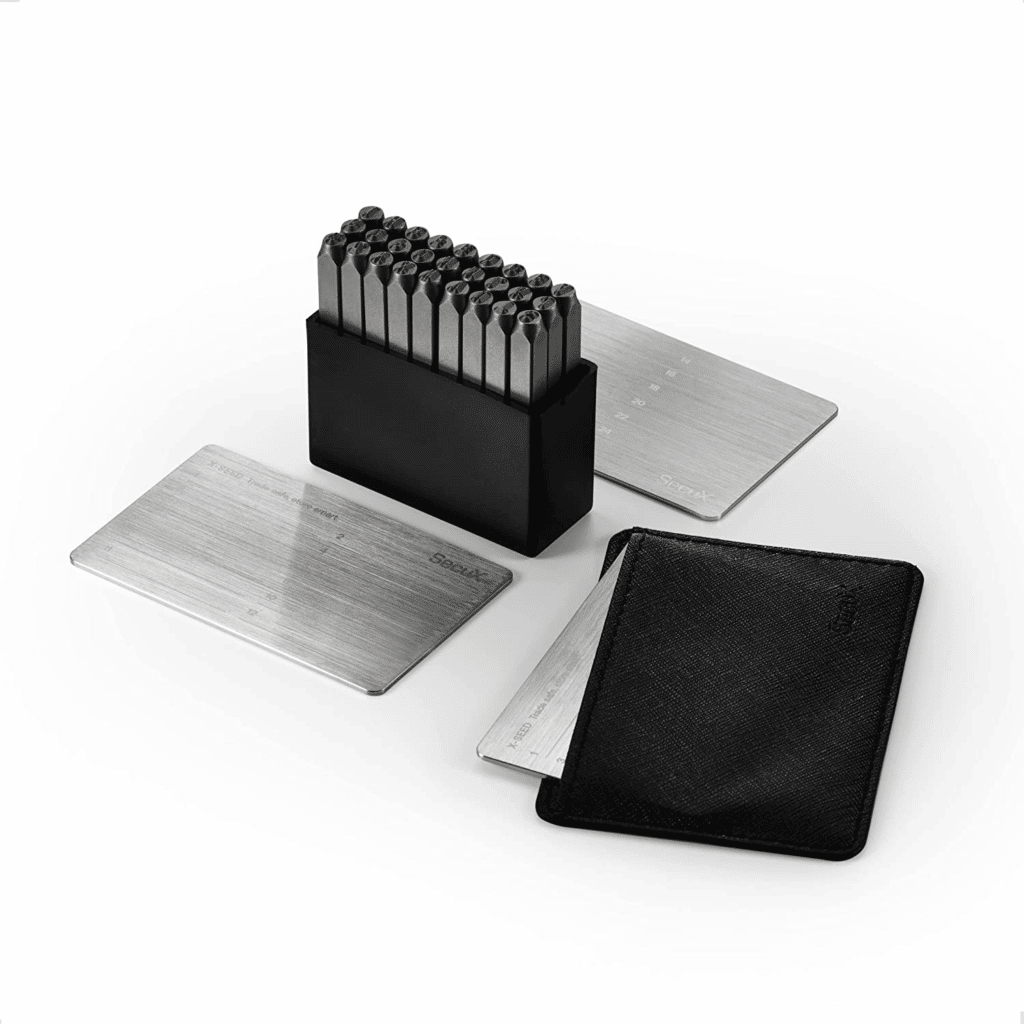
Basically, avoid having all three copies on one type of media.
This is important because maybe your ink fades. Or maybe it isn’t clear how to recover from your seed card, especially if it uses abbreviated phrases.
Last, having one copy offsite means you may store two copies in your house, but the third should be somewhere like a bank vault. This protects you in case your house is compromised by fire or theft.
Physical security
Now that you have three copies of your recovery phrase, you need to place them somewhere physically secure.
If you do not already have a safe, you can get a small, fireproof safe for less than you might think. These can be bolted to your wall somewhere out of the way, like a closet. This creates an ideal place to store your phrase.
As noted above, the ideal place for your offsite copy is in a bank vault.
Use a hardware (cold) wallet
So far, this entire post has alluded to the need for a hardware wallet, such as a Ledger or Trezor.
The alternative is a “hot wallet” or online wallet. These are enabled by software and may even run entirely from your browser. In this case, your private keys are stored on an internet-connected application. The term “hot” means connected.
Hardware wallets key your keys offline. They are cold.
Additionally, without a dedicated hardware device, you will need to violate the best practices discussed earlier about keeping your phrase entirely off of your computer or mobile device.
In addition to those two points, a hardware device adds another form of authentication. To access your crypto, it will require something you know (a password and PIN) and something you have (the physical device). This makes hacking your account dramatically more difficult. Hardware devices use this to their advantage and will have you physically confirm access, transactions, and much more.
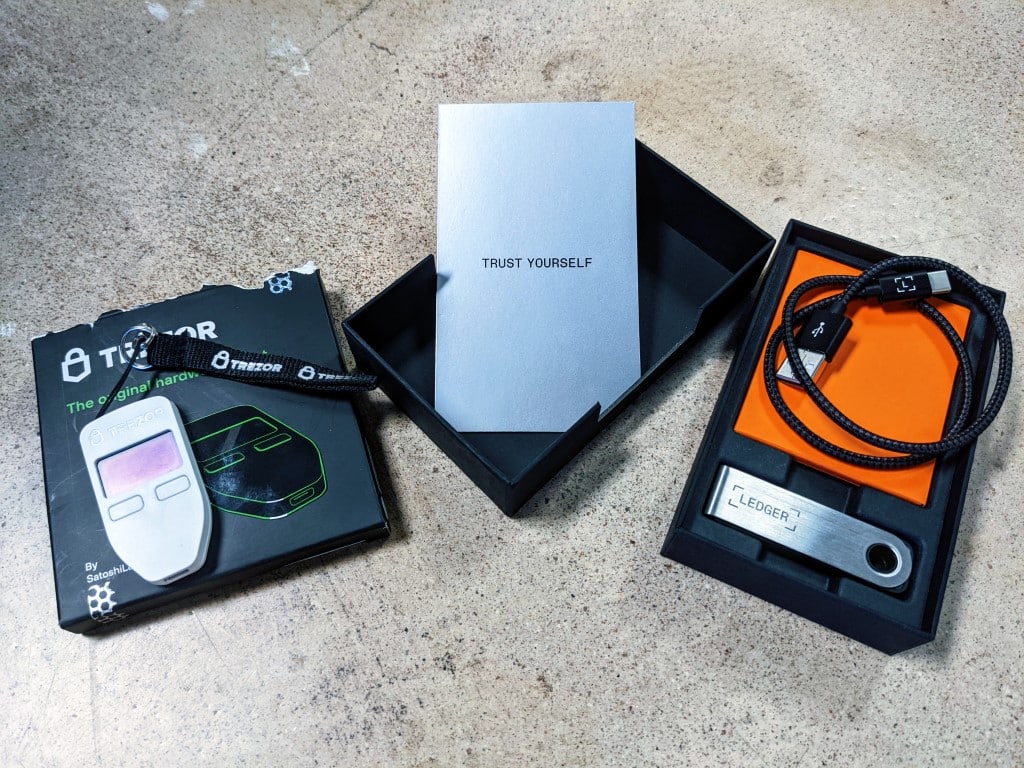
Though this does cause some inconvenience, hardware wallets are actually quite simple once you get used to them.
And don’t worry…if your hardware wallet gets lost or stops working, your crypto is fine! That’s what your recovery phrase is for.
If you suspect an issue, move your crypto
If you suspect any gap in one of the best practices above, move your crypto.
A security slip means your recovery phrase could be exposed to someone else. It may not be used today. It may not be used this year.
But if it’s floating out there, there’s the potential you will log into your wallet someday and find it empty.
You will lose sleep worrying about it. Fortunately, the fix is fairly simple.
- Move all crypto off your affected wallet to a temporary location (another wallet).
- Reset your hard wallet and set it up as new. This will remove all keys and cause it to generate a new recovery phrase.
- Test your new recovery phrase.
- Move your crypto back.
This is the only way to have peace of mind.
Additionally, even if you’re an epic HODLer, you should access your wallet once per month. You will be able to see any unexpected activity and move your crypto if something seems off.
Crypto transaction best practices
When you send crypto, your transaction is final.
That means if you mess up or are manipulated, your money will not go where you want. There are a couple of important best practices that help avoid issues.
Verify addresses
Crypto addresses are long and complex. When you enter a target address, assume two things:
- You might make a mistake. Addresses are tough on the eyes.
- The information on your screen and in your clipboard can be manipulated. These addresses have predictable patterns, so there is malicious software designed to deceive you.
So before sending a transaction, take these steps:
- It’s okay and usually best to copy-and-paste receiving addresses to avoid mistakes.
- Visually match portions of the address. Compare the one you were given with the one you pasted. Compare the beginnings. Then compare the ends. Then compare portions of the middle.
- Verify with your hardware wallet. Before sending, your hardware wallet will ask you to confirm. This step helps you avoid malicious software. The address may be altered on your screen, but won’t be altered on your hardware wallet.
Test transactions
Based on the previous step, you should have the right address. But if you’re sending a large amount of crypto, it’s best to first test with a smaller transaction. You can even break up larger moves into numerous small transactions.
This is doubly important if you’re having to deal with more complex items than just addresses. Sometimes you need to select a protocol, add a specific memo, or make other selections that you may not fully understand. Test transactions help you with this.
Educate next-of-kin
Let your crypto live forever.
Now that your wallet is secure, the final point of failure is you! If something were to unexpectedly happen, you don’t want your crypto to disappear.
With your traditional finance accounts, there will be companies and practices in place to help transition your funds. But not for your crypto.
Take time to educate your next-of-kin on how they can find, recover, and secure your crypto.
Conclusion
That’s a lot of best practices to follow, but hopefully, this helps give a good understanding of why each of these is important.
Want to get started earning yield on your crypto? See our guide How to Stake With a Ledger to Earn Crypto.
Do you have some recommended best practices? Let us know in the comments below.
Subscribe to the Newsletter
Join 7k+ working professionals to "The Five-Year Plan". Every Saturday morning, you'll receive one actionable tip to create life-changing wealth in crypto.